 Bootlin’s training courses, along with our freely available training materials, have been a cornerstone of the embedded Linux ecosystem for over 20 years. During this time, we have continuously expanded and refined our training portfolio, both to cover new technical topics and to adopt new hardware platforms for our practical lab sessions.
Bootlin’s training courses, along with our freely available training materials, have been a cornerstone of the embedded Linux ecosystem for over 20 years. During this time, we have continuously expanded and refined our training portfolio, both to cover new technical topics and to adopt new hardware platforms for our practical lab sessions.
Today, we are excited to share two closely related milestones: the availability of our major training courses on an NXP platform, and Bootlin becoming an official NXP Registered Partner. These two developments reflect our long-standing collaboration with NXP technologies and our commitment to supporting engineers working with i.MX platforms.
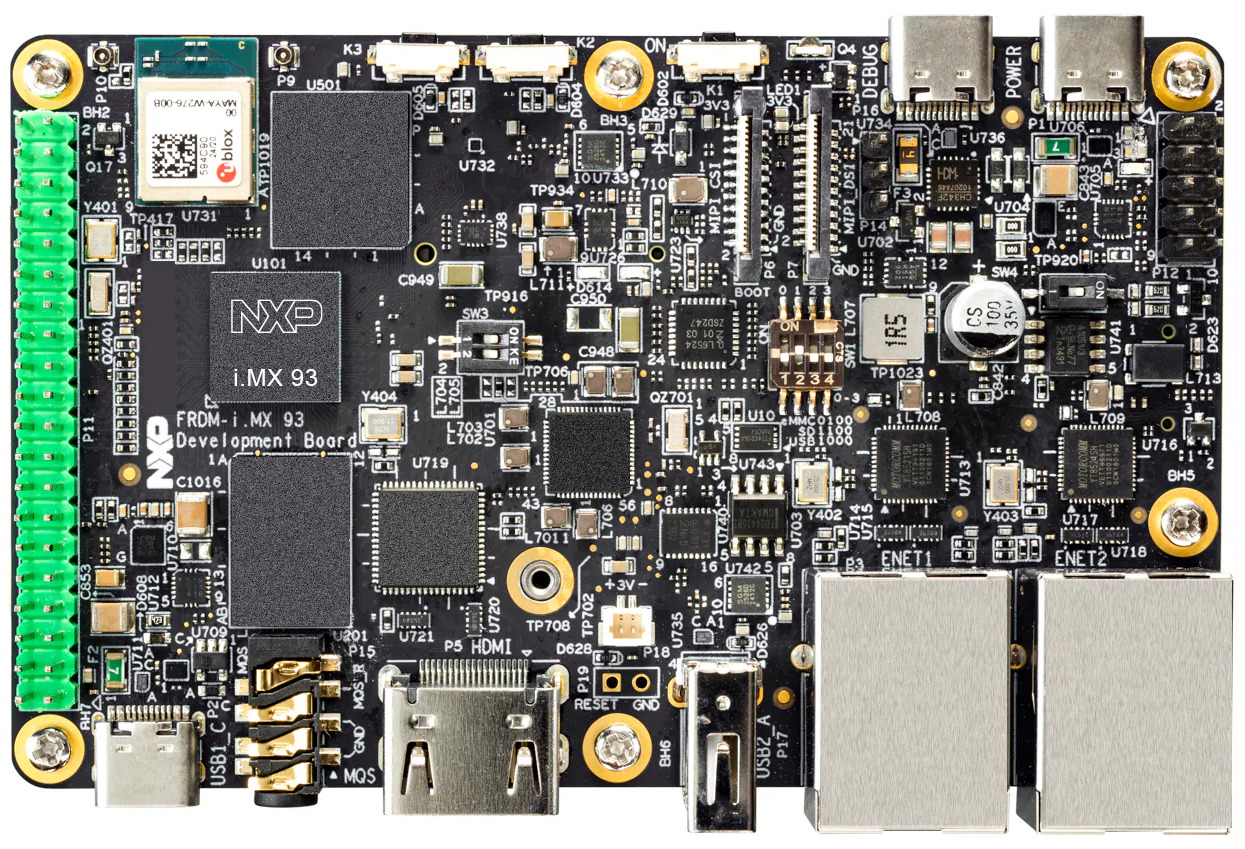
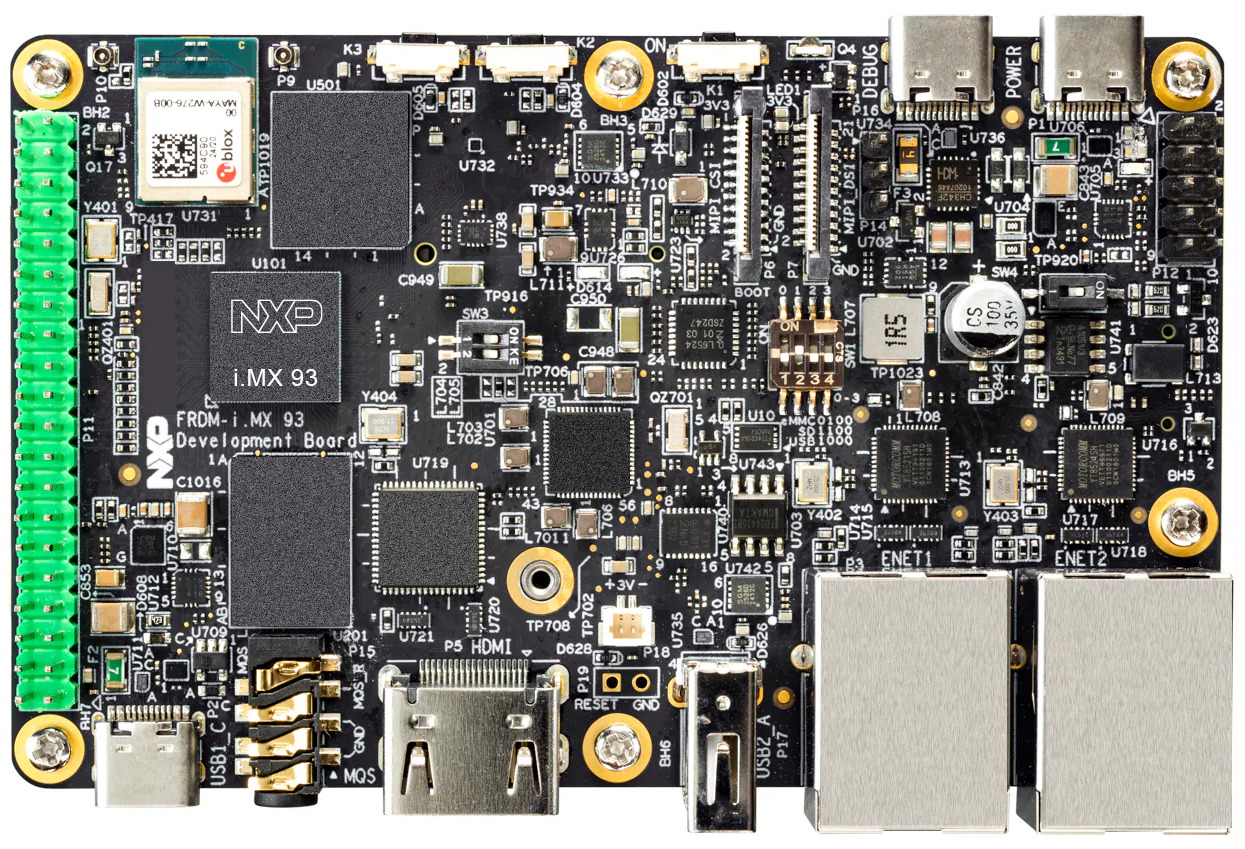 As part of our ongoing effort to improve and modernize our training offering, our three most popular training courses are now available on the NXP i.MX93 FRDM platform:
As part of our ongoing effort to improve and modernize our training offering, our three most popular training courses are now available on the NXP i.MX93 FRDM platform:
- Embedded Linux System Development
- Linux Kernel Driver Development
- Yocto Project and OpenEmbedded System Development
These courses are available immediately, and the corresponding training materials have already been published and can be freely accessed on our website. As usual, the courses can be delivered as public online sessions, private online sessions, or private on-site sessions, depending on your needs. If you are interested in attending one of these training sessions, or in organizing a private training for your team on the NXP i.MX93 FRDM platform, feel free to contact us to discuss your needs or consult our training schedule for upcoming public sessions.
Beyond training, Bootlin’s core business is providing engineering services to help organizations worldwide design and build products based on embedded Linux. Over the years, we have supported a large number of customers using NXP-based platforms—including i.MX6, i.MX7, i.MX8, and i.MX9, across a wide range of topics such as board bring-up, Linux BSP development, Linux kernel porting and driver development, Yocto Project or Buildroot integration, secure boot, and more.
Our new status as an NXP Registered Partner formally recognizes this extensive experience and collaboration. It also reinforces our ability to support customers with up-to-date expertise on NXP technologies, from early platform evaluation to production-ready systems. Check out our NXP partner page for more details on our expertise and offering related to NXP products.
In this context, making the NXP i.MX93 FRDM board a first-class platform for our training courses is a natural step. It allows engineers to train on modern NXP hardware that closely matches what they use in real-world projects, making the learning experience more practical and immediately applicable.

 Linux 7.0
Linux 7.0 

 Like most of our training courses, this one combines lectures with practical labs. The lectures are hardware-agnostic, providing knowledge applicable across platforms, with a natural focus on ARM-based systems. For the hands-on labs, we use the
Like most of our training courses, this one combines lectures with practical labs. The lectures are hardware-agnostic, providing knowledge applicable across platforms, with a natural focus on ARM-based systems. For the hands-on labs, we use the  We are pleased to announce the release of
We are pleased to announce the release of  We are pleased to announce the release of
We are pleased to announce the release of 
 Linux 6.19 was
Linux 6.19 was 